Update: 31.01.2019 – this post has been optimized to include SharePoint application health for the farm (SharePoint on-premises) and tenant (SharePoint Online).
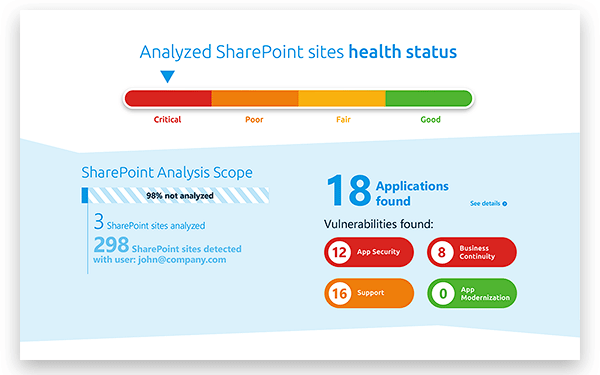
This post explains how to analyze the health of your SharePoint and how to go about conducting a full SharePoint audit of your applications.
SharePoint Health Check: Application Health
An application, regardless if it is coded, low code or no code, is used to extend or “customize” your SharePoint environment.
Many support tickets that reach the IT desk come from SharePoint applications, and it can be a real grind finding the root cause of these issues and who is responsible for fixing them. Whether these applications are on your SharePoint farm (on-premises) or SharePoint tenant (online), this task takes time and prevents users from working with SharePoint efficiently.
“78% of administrators struggle identifying if they should support a reported issue or not” (Rencore customer research, 2019).
SharePoint application monitoring, discovering and maintenance is essential for running a healthy SharePoint environment, and later in this blog we will show you steps to take when conducting a full SharePoint audit of your SharePoint applications, but a great place to start your journey would be a quick overview of your SharePoint application health, and this can be done with a free App. I recommend running the free SharePoint Application Health Check App.
SharePoint Health Check: Other good practices to consider
There are a number of good practices to consider undertaking along with a SharePoint Applications Health Check. We recommend you also consider the following for on-premises.
- Checking the servers event logs.
- Reviewing SharePoint trace logs with the ULS Viewer.
- Monitoring the Health Analyzer(check out also the additional OpenSource Health Analyzer Rules).
- Installing the latest updates and patches.
Tip: Read Todd Klindt’s blog “Hey! Should I install this SharePoint patch?” and the Bugs, Notes & Regressions of the CU/PU/SP before even considering to install any update on your farm.
Looking into the cloud(s), let it be Microsoft’s SharePoint Online or any hosted service like Rackspace orFPWeb.net, the hosting provider takes care of SharePoint infrastructure health. So usually there is not much to worry about there.
However, that does not account for SharePoint applications that are running on your tenant. Just like the SharePoint farm for on-premises, any application can have a negative impact on your SharePoint performance and security.
Tip: Follow Wictor Wilén, Spencer Harbar and Todd Klindt’s blogs who are the go-to resources for anything related to SharePoint infrastructure.
What SharePoint Applications Should I Allow
After working with SharePoint for 13 years, and I am sure most of you will agree, I can say with certainty that there is no such thing as a plain vanilla SharePoint environment. There are always coded, low-code or no-code applications used to extend the platform to achieve business needs.
When it comes to these applications, things usually get more complicated. SharePoint administrators need to not just be cautious about what they allow within their environment, but also what they currently have. When speaking to people in the SharePoint community many explain that their organization strictly forbids coded applications but allow no-code applications such as Flow and Power Apps to be used by development and business users.
The point here is all applications can negatively affect your SharePoint Health if not monitored correctly, but you should not refrain from using one or the other. Extend your SharePoint to meet the exact needs of your organization and monitor SharePoint applications on a consistent basis to keep your SharePoint environment healthy.
Auditing SharePoint Applications
This is of course where the Rencore Platform comes into place. It can be implemented for the complete production life-cycle: pre – production and production. Rencore in Pre Production covers develop, build, test and deploy. Rencore in Production covers discovering and assessing applications and teaching you how to act on those findings.
Develop
The Rencore Platform integrates with Visual Studio and Visual Studio Code to offer you contextual guidance about improving your code. With a single mouse click you can tap into the vast databases of rules that assess the quality of all kinds of SharePoint applications, from Farm Solutions to SharePoint Framework applications. Because you can analyze your code directly inside your developer tools, you save time and don’t lose the context of your work.
 Build
Build
The Rencore Platform integrates with your existing build systems, such as Visual Studio Team System, Azure DevOps, TeamCity, Jenkins or Atlassian Bamboo so that you can automate quality assessment and ensure that your applications meet your organization’s quality criteria.
 Test & Deploy
Test & Deploy
No matter if you build SharePoint applications in-house, outsource the development, or purchase applications from vendors, using the Rencore Platform you can analyze them before deploying them in production and ensure that they don’t pose any risks to your organization. You can perform the analysis either manually or integrate it in your deployment process using for example PowerShell.
 Discover
Discover
The Rencore Platfrom continuously monitors your SharePoint environment for new and changed applications ranging from scripts, forms and workflows to applications built by professional developers. It builds up an inventory of the discovered applications which you can then explore via your personal portal. The gathered data doesn’t include any confidential information and is accessible only to your organization.
 Assess
Assess
After discovering SharePoint applications, the platform analyzes them against its vast database of rules. We detect if your applications contain any known vulnerabilities or pose other security, performance or business continuity risks to your organization. For high-risk anomalies you can configure alerts to get notified as soon as they are discovered.
 Act
Act
All findings are presented in dynamic reports which you can use to get additional details and draw an action plan to mitigate discovered risks. The reports vary from high-level overview, suitable for executives, to detailed findings required by developers to fix discovered issues.
 Take the next step
Take the next step
So what stage are you currently at? Are you just getting started and looking to delve deeper into your SharePoint applications? I recommend you try the free SharePoint Applications Health Check App.
Are you further into understanding SharePoint health and are considering the next steps to fix your SharePoint application issues? Then why not see how the Rencore Platform can help and take a live product tour.



