Most organizations require that their information systems and data can survive a disaster. To accomplish these, IT Managers are executing disaster-recovery projects. These projects help to identify critical information systems, tasks, and processes. The primary objective is to answer the question “How quickly can we recover after a disaster?” A Risk Assessment on the other side helps to identify potential threats.
The Risk Assessment
An essential requirement for conducting a disaster-recovery project is performing a business impact analysis (BIA). A business impact analysis (BIA) is a systematic process by which an organization gathers and analyzes information about essential functions and operations. The information is then used to determine how the organization would be interrupted by a disaster. Performing a business impact analysis (BIA) provides an organization with reliable data concerning potential impacts, costs of disasters, as well as defining recovery priorities and strategies. It can also help a Chief Information Officer, Chief Security Officer, Security, and IT Teams answer some significant questions:
- Which information systems and processes are crucial to the continuation of the organization?
- How quickly must critical information systems and operations be resumed before notable or unacceptable losses occur?
- What are the dependencies among different information systems and processes?
- What order and how fast do specific information systems need recovering after a disaster?
- What information systems pose the most risk?
- The most significant threats to the organization?
Once a business impact analysis (BIA) is performed within the organization, having analyzed critical information systems, reviewed business functions and identified the impact a loss of those functions, the next step is to conduct an IT and Security risk assessment.
Just like “bad actors” the first step in performing a risk assessment is to gather information about potential threats to the organization. These must include System (Hardware, Software, and Data), Business and Natural-related (Weather Service Data and Geological) information. Once you have all the information, identifying threats for the organization is critical. Common threats that could impact the business are not just IT and Security related. A larger Risk Assessment includes natural disasters, such as floods, earthquakes, environmental threats, such as long-term power failure and pollution. After identifying potential threats, you can then assess any weaknesses in IT systems, that could allow potential risks to become full-blown disasters.
IT and Security Risk Assessment
Assessing potential security risks and threats is an integral part of any organizations Security posture. Risk assessment is essential for IT and Security departments that control network, servers, data, and access control. The purpose of the IT risk assessment is to help identify potential threats that could expose data or other information outside of the organization.
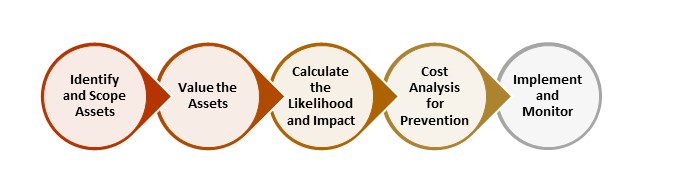 An IT risk assessment fundamentally is completed to answer the following five questions:
An IT risk assessment fundamentally is completed to answer the following five questions:
- What are the critical technology assets, that a security or data breach would impact the most?
- What are the business processes that use or require the information?
- What threats could affect the ability for the business processes to function?
- What are the weak endpoints within critical applications, network, and systems?
- Would we as an organization be able to identify a Security or Data Breach?
Two of the highest priority IT and Security risks recognized during the risk assessment are: “Accidental User Behavior” and “Malicious User Behavior.” These two terms relate to the employees within the organization. All employees are potential threats; mistakes happen accidentally. Tasks such as deleting important files, clicking malware links, or damaging a piece of equipment are quite common risks for all organizations. There are also those users that perform malicious behavior such as deleting data, executing a distributed denial of service (DDOS) attack, stealing data, misuse of someone else’s credentials, or even stealing a computer or server. All of these potential risks and threats need to be analyzed and assessed.
The Risk of Cloud Services
More recently an area of significant concern comes from client-side development technologies used within web-based applications. Many vendors provide their services and platforms via the web. On the one hand, the infrastructure hides behind a data center firewall, but for the user experience, it can become less secure as it could be easily modified. The risk comes from end users who have the access rights needed to embed client-side code directly into a platform for extensibility.
In June 2018, Ticketmaster suffered a significant security breach, which led to the possible leak of tens of thousands of credit card details. A well-known British security researcher Kevin Beaumont stated: “the breach had been caused by Ticketmaster directly applying a customized piece of JavaScript without notifying its support team (Inbenta).” This Security and Data Breach highlights that a simple deployment mistake can lead to significant risks.
Including this type of assessment within a normal IT and Security risk assessment will help mitigate these risks. Combined with this type of evaluation are vulnerability checks. A vulnerability is a weakness in a system that could be used to breach security and harm your organization. Identifying these is done through vulnerability analysis, audit reports, checks against vulnerability databases, validation with vendor data as well as checking with commercial computer incident response teams, and system software security analysis.
Next, with potential risks identified the probability that an identified vulnerability might be exploited needs to be understood. Not every vulnerability is exploitable easily, and some are complicated or even impossible to use. Based on the type of weakness, the capability, and motivation of the threat source, as well as the existence and effectiveness of controls you have in place, dictate the threat level. Rather than assigning a numerical value, many organizations utilize categories such as High, Medium and Low to assess the likelihood of an attack or adverse event taking place.
High – Corrective measures need developing as soon as possible.
Medium – Corrective measures need developing within a reasonable period.
Low – Organization must decide whether to accept the risk or implement corrective actions.
These potential risks, of course, are hypothetical based on a perceived threat.
We use Office 365, why should we perform a Risk Assessment?
Office 365 is a robust cloud offering provided by Microsoft, containing various services and components. It is one of the largest cloud platforms in the world and protected by Microsoft. The answer to that is “Yes,” “Yes” it is. If you look at the Trust Center site provided by Microsoft to learn about the mitigations that are in place, you will see that indeed there are significant protections in place.
MS Trust Center: Office 365 Security
Just looking at Office 365 itself there are many capabilities available to help protect.
- Multi-Factor Authentication
- Role Based Access Control
- Alerts and Security Notifications
- Investigation and Audit Log Searching
- Advanced Threat Protection
- Single Sign-On using Azure Active Directory and AD Connect
- Mobile Device Management
- Conditional Based Access Controls and Policies
- Data Loss Prevention and Protections
- Secure Score
All of these components offer great Security controls when enabled and mitigate many of the risks that organizations face today. So, with all of these great features, why perform a risk assessment? Remember, that a risk assessment is about isolating the risks and potential threats and providing mitigations. It is the same in the cloud too. Microsoft themselves perform risk assessments to ensure they have all the rights plans, contingencies and protections in place for organizations. However, Microsoft does not mandate how an organization uses the services, that is left to the business to decide. At this point that is when a risk assessment is needed. Based on our understanding of employees “Accidental User Behavior” and “Malicious User Behavior,” we need to inspect continually, monitor and assess the implementation as it changes over time.
Performing a risk assessment for Office 365 is about validating current Security Controls and Practices. Using and following the Secure Score will go a long way to creating a better Security Posture. However, there are areas not covered within the core Security Controls, such as Applications or Customization’s added like those that caused the breach for Ticketmaster. Microsoft does not want to limit the customization options for creating applications, as such, the organization must control and manage the potential risks that come from the extensibility offered within the platform. The following links outline some of the reasoning and technical details of why this type of risk assessment is required.
- Security Features missing from Office 365
- What Does Risk Prevention Mean Inside SharePoint
- Is JavaScript Safe for SharePoint?
Performing a risk assessment of a cloud service such as Microsoft 365 is now more critical than ever before. Combining this with the evaluation of the On-premises services that are in use allows you as an organization to understand the full threat landscape. The risks and vulnerabilities to the organization will change over time; however, if the organization continues to follow a risk assessment methodology, it will be in an excellent position to address any new risks and vulnerabilities that arise.
Understand why you need a Risk Assessment
Understanding why you need to perform this level of Risk Assessment is imperative. If you are not sure, ask yourselves these questions:
- Do I know where all the customizations are within my Office 365 Tenant?
- Do I know how many Script Editor web parts are on the site?
- Do I know where custom JavaScript is on pages?
- Do I know who made configuration changes last?
- Is my Tenant configured for the best Security?
- Do I know what the code is doing on my site?
And check out Rencore to help you find answers.
If you would like to understand how to get a centralized and automated approach to collecting, assessing, and acting on data in your Office 365 tenant then the following whitepaper is a must read! Download a copy of Complete visibility across Microsoft 365 for free today.



